STRATEGY INDEX
- Mission Briefing: The Gravity of Instagram Account Compromise
- Vector 1: The Art of the Phishing Scheme - Deceptive Login Pages
- Vector 2: Brute Force & Credential Stuffing - The Password Guessing Game
- Vector 3: Social Engineering - Hacking the Human Element
- Vector 4: SIM Swapping & Account Takeover
- The Arsenal of the Digital Operative: Essential Defensive Tools
- Comparative Analysis: Common Attack Vectors vs. Robust Defenses
- Debriefing & Your Next Mission: Fortifying Your Digital Fortress
In the digital realm, few platforms command as much daily attention as Instagram. It's a vibrant ecosystem for connection, creativity, and commerce. But beneath the polished interface lies a landscape ripe for exploitation. Cybercriminals are constantly devising new and sophisticated methods to breach accounts, steal data, and disrupt lives. This dossier, codenamed "Operation: Digital Fortress," is your comprehensive intelligence brief on how Instagram accounts are compromised and, more importantly, how you can build an unbreachable defense. Forget the sensationalism; we're dissecting the mechanics of these attacks to equip you with actionable intelligence.
Mission Briefing: The Gravity of Instagram Account Compromise
Understanding the "why" is crucial. Instagram accounts are not merely social hubs; they are repositories of personal memories, business assets, communication channels, and increasingly, financial tools. A compromised account can lead to:
- Identity theft and reputational damage.
- Financial loss through fraudulent transactions or scams.
- Unauthorized access to linked accounts (email, other social media).
- Dissemination of malicious content or misinformation.
- Blackmail and extortion.
The methods employed by attackers are diverse, evolving, and often exploit human psychology as much as technical vulnerabilities. This report will illuminate these tactics, transforming potential victims into informed defenders.
Vector 1: The Art of the Phishing Scheme - Deceptive Login Pages
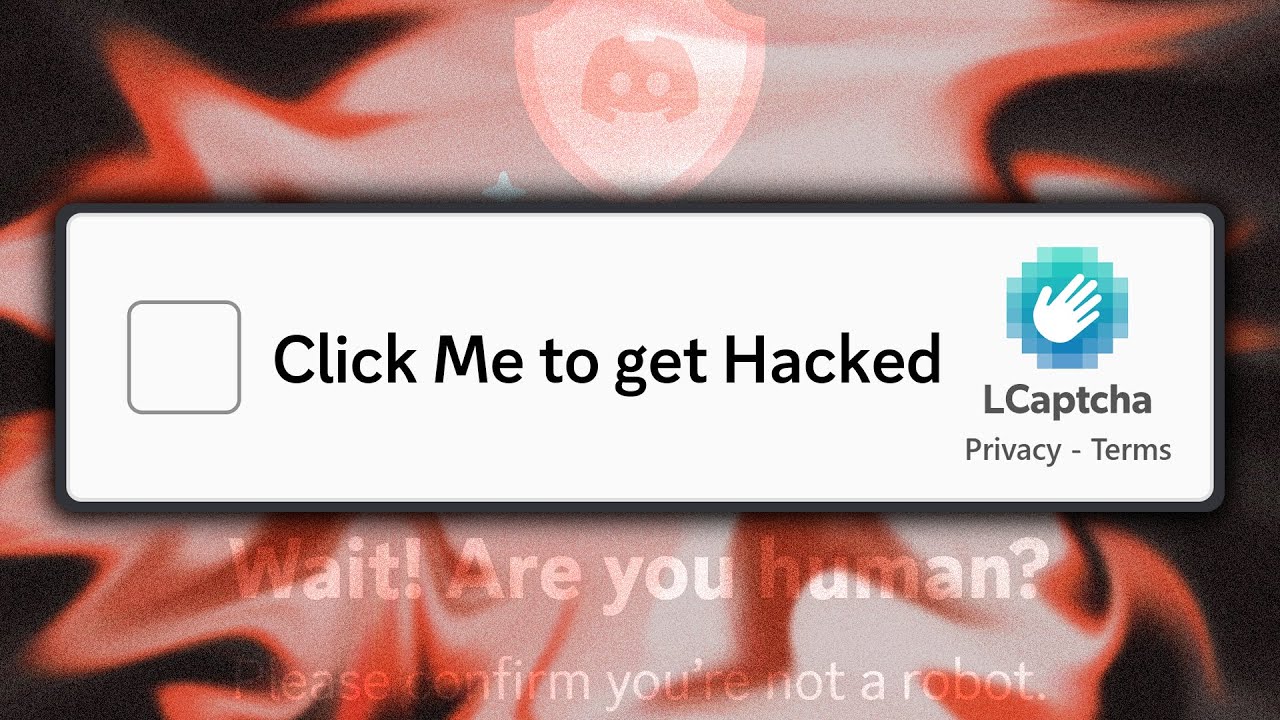
"The Fake Login Page That Steals EVERYTHING!" This is perhaps the most prevalent and deceptively simple attack vector. Attackers create a meticulously crafted replica of Instagram's legitimate login page. The goal? To trick users into entering their username and password, which are then sent directly to the attacker.
"Phishing attacks often prey on urgency and trust. A fake email or direct message might claim your account has been flagged for suspicious activity, requiring immediate verification via a provided link. The link leads to a page that looks identical to Instagram's login, but it's a trap."
Technical Breakdown:
- Domain Spoofing: Attackers register domain names that closely resemble Instagram's legitimate domains (e.g.,
instagram-login.com,instagrram.net). - HTML/CSS Replication: The fake login page is built using standard web technologies to mimic the original's look and feel.
- Server-Side Scripting: A backend script (often in PHP, Python, or Node.js) captures the submitted credentials and stores them for the attacker.
- Delivery Mechanisms: These pages are distributed via malicious emails, SMS messages (smishing), social media direct messages, or even malicious advertisements.
Defense Protocol:
- Verify URLs Religiously: Always check the URL in your browser's address bar. Look for typos, extra characters, or unusual domain extensions. Instagram's official domain is
instagram.com. - Enable Two-Factor Authentication (2FA): This is your most potent defense. Even if your password is stolen, 2FA provides an additional layer of security.
- Be Skeptical of Links: Never click on suspicious links in unsolicited messages. If you need to log in, go directly to the official website by typing the URL yourself.
- Utilize Password Managers: Password managers often auto-fill credentials only on legitimate sites, flagging fake ones.
Vector 2: Brute Force & Credential Stuffing - The Password Guessing Game
"They're Guessing Your Password RIGHT NOW!" This method involves automated software attempting to log in to an account by trying a vast number of username and password combinations. This includes:
- Brute Force Attacks: Systematically trying every possible character combination. This is computationally intensive but can be effective against weak passwords.
- Dictionary Attacks: Using lists of common passwords (e.g., "password123", "12345678") or words found in dictionaries.
- Credential Stuffing: This is a highly effective technique where attackers use lists of username and password combinations stolen from data breaches on other websites. They assume users reuse passwords across multiple platforms.
"The phrase 'password123' or 'qwerty' might seem absurdly weak, yet they persist on lists used by attackers. If you reuse passwords, a breach on a minor forum could inadvertently grant access to your Instagram."
Defense Protocol:
- Strong, Unique Passwords: Create long (12+ characters), complex passwords using a combination of uppercase letters, lowercase letters, numbers, and symbols. Never use personal information.
- Password Manager: A password manager can generate and store highly unique and complex passwords for every online service.
- Regularly Change Passwords: Especially if you suspect a breach or if Instagram or other services notify you of a compromise.
- Monitor for Breaches: Use services like "Have I Been Pwned" to check if your credentials have appeared in known data breaches.
Vector 3: Social Engineering - Hacking the Human Element
"They're Hacking Your Brain, Not Your Account." Social engineering exploits human psychology rather than technical flaws. Attackers manipulate individuals into divulging sensitive information or performing actions that compromise their security.
- Pretexting: Creating a fabricated scenario (a pretext) to gain trust. An attacker might pose as an Instagram support agent, a friend in distress, or a representative from a service provider.
- Baiting: Offering something enticing (e.g., "free Instagram followers," exclusive content) in exchange for login credentials or personal information. This is often seen in schemes promising "free followers."
- Quid Pro Quo: Offering a supposed service or benefit in exchange for information. For example, claiming to help "verify" an account in exchange for login details.
"The allure of 'free followers' or 'account verification' is a powerful lure. These are classic baiting tactics. No legitimate platform will offer such services for free, and certainly not by asking for your password directly."
Defense Protocol:
- Verify Identity: If someone claims to be from Instagram support or another authority, do not trust them implicitly. Contact the organization directly through their official channels to verify the request.
- Be Wary of "Too Good to Be True" Offers: Free followers, premium features for free, or easy account recovery often mask malicious intent.
- Educate Yourself and Your Network: Understanding these psychological tactics is the first step to resisting them. Share this knowledge.
- Trust Your Intuition: If a request feels off, suspicious, or overly demanding, it probably is.
Vector 4: SIM Swapping & Account Takeover
"They Stole My Phone Number To Hack My Instagram!" SIM swapping is a more advanced attack where a cybercriminal convinces a mobile carrier to transfer the victim's phone number to a SIM card controlled by the attacker. This allows them to intercept calls and SMS messages, including the codes used for password resets and 2FA.
How it Works:
- Information Gathering: Attackers collect personal information about the victim (often obtained through previous breaches or social engineering) to impersonate them with the mobile carrier.
- Social Engineering the Carrier: The attacker contacts the mobile provider, claiming their SIM card is lost or stolen, and requests a transfer of the victim's number to a new SIM they possess.
- Intercepting Codes: Once the number is transferred, all incoming calls and SMS messages, including those from Instagram for password resets or 2FA codes, are routed to the attacker.
- Account Takeover: The attacker uses these intercepted codes to reset the Instagram password and gain full control of the account.
Defense Protocol:
- Secure Your Mobile Account: Add a strong PIN or password to your mobile carrier account. Request that additional security measures (like an account PIN) be required for any SIM changes.
- Be Cautious About Sharing Personal Information: Especially details that could be used to impersonate you with your phone provider.
- Monitor Your Phone Service: Be alert for any sudden loss of service, which could indicate a SIM swap. Contact your carrier immediately if this happens.
- Use Authenticator Apps for 2FA: Apps like Google Authenticator or Authy generate time-based codes that are not sent via SMS, making them immune to SIM swapping.
The Arsenal of the Digital Operative: Essential Defensive Tools
To operate effectively in the digital space and defend your assets, you need the right tools. This isn't about offensive capabilities, but about robust, proactive security.
- Password Manager: 1Password, Bitwarden, LastPass. Essential for generating and storing unique, strong passwords.
- Two-Factor Authentication (2FA) App: Google Authenticator, Authy. Provides a more secure alternative to SMS-based 2FA.
- Reputable Antivirus/Anti-Malware Software: Ensure your devices are protected against malicious software that could steal credentials.
- VPN (Virtual Private Network): For added privacy and security, especially on public Wi-Fi. Consider reputable providers like NordVPN or ExpressVPN.
- Breach Monitoring Services: Have I Been Pwned. Stay informed if your details appear in data leaks.
Comparative Analysis: Common Attack Vectors vs. Robust Defenses
Let's map the primary threats against their most effective countermeasures:
| Attack Vector | Primary Defense Mechanism | Secondary Defense Mechanism |
|---|---|---|
| Phishing (Fake Login Pages) | URL Verification & Browser Security Features | Skepticism towards Links & Password Manager Auto-fill |
| Brute Force/Credential Stuffing | Strong, Unique Passwords & Password Manager | Two-Factor Authentication (2FA) |
| Social Engineering (Baiting, Pretexting) | Critical Thinking & Verification of Identity | Awareness of "Too Good to Be True" Offers |
| SIM Swapping | Securing Mobile Carrier Account (PIN/Password) & Using Authenticator Apps for 2FA | Monitoring Phone Service for Interruptions |
The overarching theme? A layered defense is paramount. Relying on a single security measure is like leaving one side of your fortress unguarded.
Debriefing & Your Next Mission: Fortifying Your Digital Fortress
The digital landscape is a constant battleground. Attackers are resourceful, persistent, and innovative. However, by understanding their methods—the deceptive login pages, the relentless password guessing, the manipulation of human psychology, and the sophisticated SIM swap attacks—you gain the power to defend yourself effectively.
This intelligence dossier has equipped you with the knowledge of common attack vectors and the corresponding defensive protocols. Remember, the most sophisticated technology is useless without user vigilance. Your awareness is your first and strongest line of defense.
Your mission, should you choose to accept it, is to implement these defenses immediately.
Your Mission: Execute, Share, and Debate
If this blueprint has armed you with critical knowledge and saved you potential hours of work, share it across your professional networks. Knowledge is a tool, and this guide is an essential piece of your operational kit.
Know someone navigating the murky waters of online security? Tag them below. A true operative doesn't leave a comrade behind.
What threat vectors concern you most? What are your go-to defensive strategies? Demand our analysis on the next threat in the comments. Your input dictates the next mission briefing.
Have you successfully implemented these defenses? Share your success stories and tag us. Intelligence must flow.
Mission Debriefing
Execute the steps outlined. Discuss them. Your active participation strengthens the collective digital defense.
About The Cha0smagick
The Cha0smagick is a seasoned digital operative, a polymath in technology, and an elite ethical hacker with deep experience in the trenches of cybersecurity. With a pragmatic, analytical, and slightly cynical outlook forged from auditing 'unbreakable' systems, The Cha0smagick transforms complex technical data into actionable intelligence and robust solutions. This blog serves as a repository of 'dossiers' for a select group of digital operatives, providing the blueprints needed to navigate and secure the modern digital frontier.
For comprehensive financial security and asset diversification in the digital age, exploring robust platforms is key. A smart strategy involves diversifying your approach to digital assets. To that end, consider opening an account on Binance and exploring the crypto ecosystem.
Related Dossiers:
- Phishing Defense Strategies
- Password Security Best Practices
- Implementing Two-Factor Authentication
- Understanding Social Engineering Tactics
- Preventing SIM Swap Attacks
- Essential Cybersecurity Tools
Frequently Asked Questions
1. Can Instagram accounts be hacked easily?
While Instagram invests heavily in security, sophisticated attackers can exploit vulnerabilities through methods like phishing, credential stuffing, and social engineering. Ease depends on the target's security practices and the attacker's resources.
2. Is it illegal to try and hack an Instagram account?
Yes, attempting to access any account without explicit authorization is illegal and unethical. This guide focuses on understanding these methods for defensive purposes only.
3. What is the best defense against Instagram hacking?
A multi-layered approach is best: strong, unique passwords managed by a password manager, robust Two-Factor Authentication (preferably via an authenticator app), and extreme skepticism towards unsolicited links and offers.
4. How do I know if my Instagram account has been hacked?
Signs include unusual login activity, posts or messages you didn't send, changes to your profile information, or being logged out and unable to reset your password.
Trade on Binance: Sign up for Binance today!